Behind the Screen: Lessons from Undercover Work in the Cyber Underground
April 29, 2026I recently had the opportunity to join Jon Taber for an in-depth discussion about my career in cybercrime investigations, undercover operations, and the evolving threat landscape organizations face today.
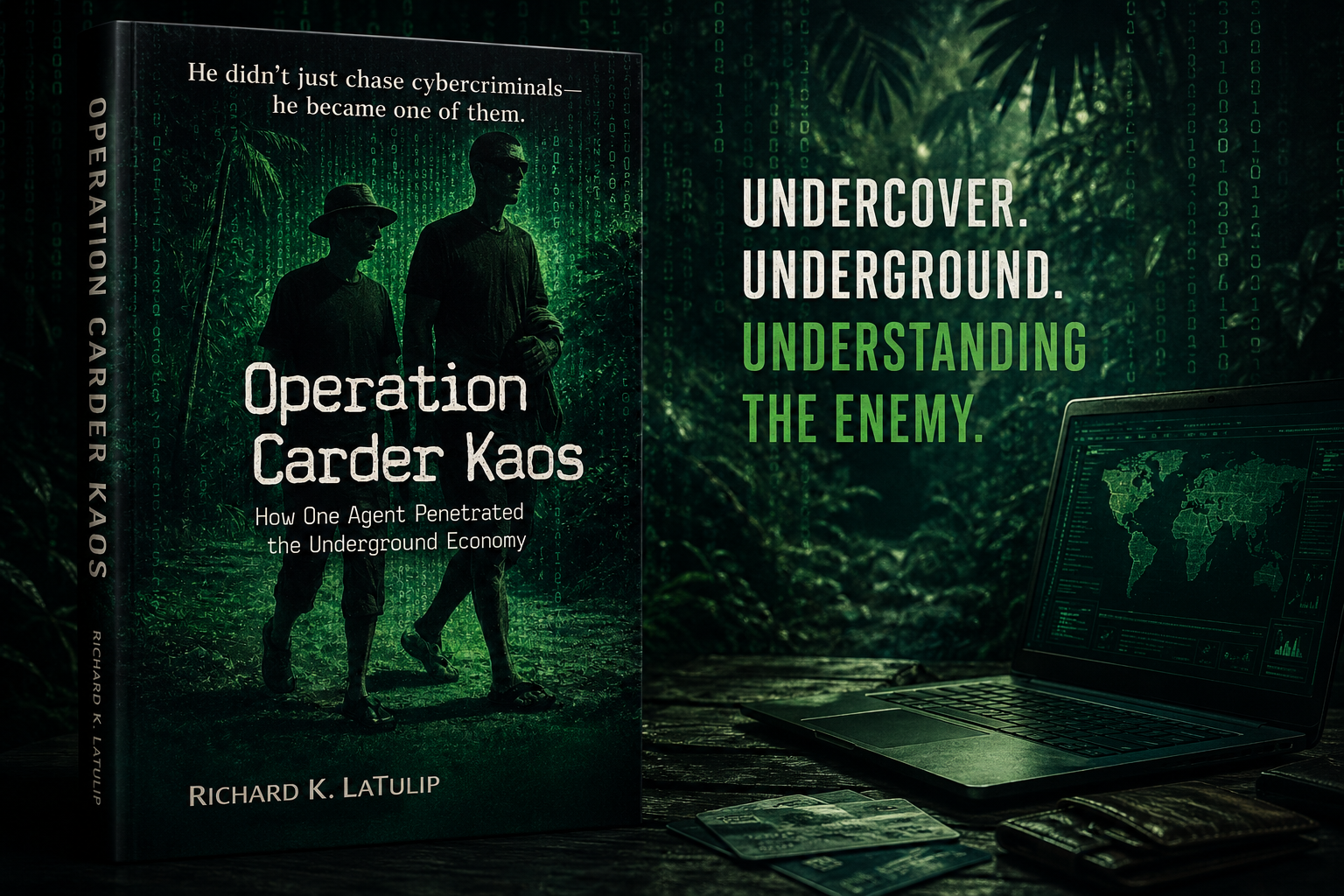
During the conversation, we explored my experiences as a former U.S. Secret Service agent working undercover in cybercrime investigations during a time when online criminal communities were rapidly expanding and becoming increasingly sophisticated. We discussed how trust, identity, reputation, and deception operated within underground forums, and how those same concepts continue to influence today’s cyber threat environment.
One of the central themes of the discussion was that while technology continues to evolve, many cyber threats still fundamentally revolve around people. Social engineering, identity compromise, manipulation, and trust exploitation remain some of the most effective tactics used by adversaries. The tools may change, but human behavior remains a primary attack surface.
We also discussed how organizations must move beyond a prevention-focused mindset. Cyber resilience requires organizations to understand adversaries, identify operational dependencies, and apply timely, relevant, and actionable intelligence to reduce risk and improve decision-making. Intelligence becomes most valuable when it helps organizations anticipate threats, prioritize action, and recover quickly when incidents occur.
The conversation also touched on:
- The evolution of cybercriminal ecosystems
- Undercover operational tradecraft
- Intelligence-driven security strategies
- Advanced social engineering tactics
- Identity-focused attacks
- Enterprise risk and resilience
- Lessons learned from real-world investigations
I appreciate Jon Taber for the opportunity to participate in this thoughtful discussion and for creating a platform that enables meaningful conversations about cybersecurity, leadership, and resilience.
If you are interested in cybersecurity, cybercrime investigations, intelligence, or leadership in high-pressure environments, I encourage you to listen to the episode.